Isolated Architecture PCS SIS Fully Independent Safety System
🧱 Isolated Architecture PCS SIS Fully Independent Safety System
Isolated Architecture PCS SIS When Separation Isn’t Just Best Practice — It’s the Difference Between a Close Call and a Catastrophe
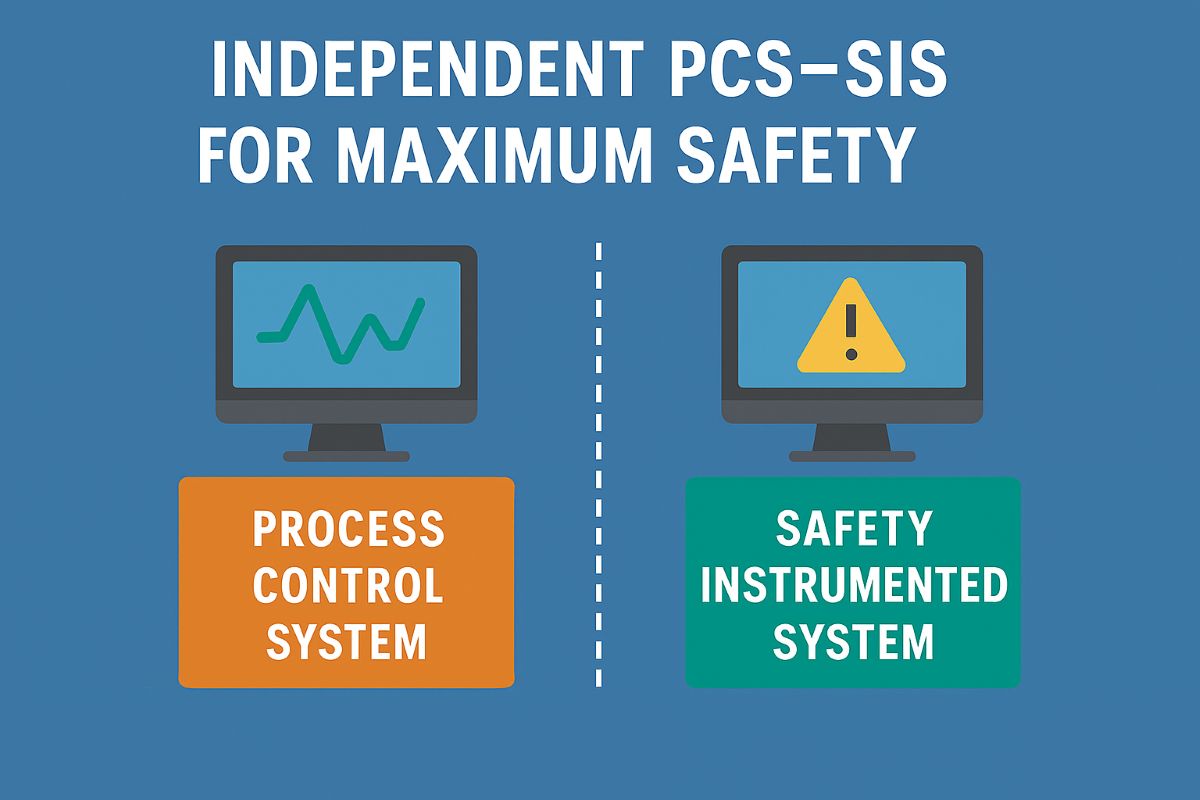
In safety-critical industries, the phrase “don’t put all your eggs in one basket” isn’t a cliché — it’s an engineering mandate. Isolated Architecture, where the Process Control System (PCS) and Safety Instrumented System (SIS) operate as completely independent entities, is the gold standard for high-hazard environments. Let’s unpack why. 🔍
⚠️ When to Choose Isolated Architecture: High-Hazard Scenarios & Regulatory Drivers
Not every plant needs total separation — but some absolutely cannot afford anything less. Isolated Architecture is the mandated or strongly recommended choice when a single point of failure could trigger irreversible consequences.
- 🏭 Oil & Gas Refineries — High-pressure vessels, flammable hydrocarbons, and exothermic reactions demand fully independent safety layers
- ☢️ Nuclear Power Plants — Reactor shutdown systems must be immune to control system faults, per IEC 61513
- ⚗️ Chemical Manufacturing — Toxic gas release scenarios classified as SIL 3 or SIL 4 require isolation by design
- ✈️ Offshore Platforms — Fire & gas detection systems follow API 505 and IEC 61511, requiring hard independence
- 💊 Pharmaceutical & Biopharma — FDA 21 CFR Part 11 compliance mandates audit-separated safety control layers
Regulatory drivers are equally powerful. Standards like IEC 61511 (Functional Safety for Process Industry) and OSHA PSM 29 CFR 1910.119 explicitly push — and in many cases require — SIS independence for higher Safety Integrity Levels (SIL 2 and above). If your process falls under a Major Hazard Regulation, isolation isn’t optional — it’s audited. 📋
⚖️ Advantages & Limitations of Fully Independent SIS — Reliability vs. Cost
Isolated Architecture is powerful, but it comes with real trade-offs every safety engineer must weigh honestly.
✅ Advantages
- 🟢 Zero common-cause failures between PCS and SIS
- 🟢 Independent testing and validation cycles keep integrity uncompromised
- 🟢 Regulatory compliance at SIL 2/3 is far easier to demonstrate
- 🟢 A PCS cyberattack cannot cascade into the SIS
- 🟢 Faults in SCADA/DCS cannot mask or suppress safety-critical alarms
❌ Limitations
- 🔴 Higher CAPEX — duplicate sensors, logic solvers, cabling, and panels
- 🔴 More complex maintenance schedules and spare-part inventory
- 🔴 Operator training burden increases significantly across two separate systems
- 🔴 Data integration for reporting requires purpose-built, secure one-way links
- 🔴 Risk of alarm fatigue if SIS and PCS alarm philosophies aren’t carefully harmonized
💡 The bottom line? Isolated architecture trades short-term cost efficiency for long-term reliability and demonstrable safety integrity. For high-consequence processes, that trade is always worth it.
🔥 Case Study: Texas City Refinery Explosion (2005)
How Lack of Proper SIS Independence Contributed to the Disaster
💀 15 Workers Killed | 180+ Injured | $1.6 Billion in Total Losses
On March 23, 2005, the isomerization unit at BP’s Texas City refinery exploded during a routine restart procedure. The U.S. Chemical Safety Board (CSB) investigation revealed a devastating truth: level indicators had failed, alarms were suppressed within the DCS, and the safety layer had no meaningful independence from the process control environment.
The raffinate splitter tower was catastrophically overfilled — operators couldn’t clearly differentiate between DCS process readings and genuine safety-state data. High-level alarms that should have triggered a hard shutdown were either muted, bypassed, or drowned in a flood of nuisance alerts from the same integrated system.
Had the SIS been fully isolated — with its own dedicated level transmitters, independent logic solver, and hard-wired shutdown triggers that no DCS operator could override — the automatic protective action could have intervened before the tower overpressured and vented flammable liquid into the atmosphere. 🧯
🚨 Key Lesson
Integration convenience killed 15 people. When PCS and SIS share sensors, networks, or alarm management, a single operator error or software fault can silently disable both layers simultaneously. Independence is not redundancy — it is a completely separate line of defense.
🔒 Cybersecurity Benefits of Isolation — Air-Gapped Systems & Their Practical Challenges
In an era of OT cyberattacks — from Stuxnet targeting centrifuge logic to the Oldsmar water treatment breach — isolated SIS architecture has become a cybersecurity strategy, not just a safety philosophy. 🛡️
- 🔌 Air-gapped SIS — No network path means no remote exploit vector; ransomware on the DCS cannot reach the shutdown system
- 🔁 One-way data diodes — Allow SIS health data to flow to historians without creating a return path for attackers
- 🧱 Separate engineering workstations — SIS logic changes require physical access, eliminating remote tampering entirely
- 📵 No USB / removable media policy — Isolated networks demand strict physical security hygiene at every access point
But air-gapping brings practical headaches. Firmware updates must be applied manually on-site. Diagnostics require physical presence. Modern IIoT dashboards struggle to surface SIS health data without purpose-built unidirectional gateways. And the constant organizational pressure to “just connect it to the cloud” is the silent enemy of every air-gapped installation. 🌐
The answer? Treat every request to integrate the SIS into a shared network as a formal Management of Change (MOC) event, subject to full SIL verification review. The inconvenience is the point — friction protects. 🔐
🧱 Final Thought: Independence Is Not a Luxury — It’s a Firewall for Human Lives
Isolated Architecture costs more to build and maintain. It demands more from engineers, operators, and management alike. But when the process you’re controlling can kill in seconds, the architecture itself is your last line of defense.
Don’t compromise it for convenience. Ever. 🔒